Before, trying to understand about the certificate management, installation of certificates inside the WebSphere application server we should first understand why we need ssl communication and what is the impact of not installing the certificates.
During the olden days whenever we want to make any banking transaction (e.g.: depositing the money, with draw money, transfer money, etc), make a reservation for Air travel, etc… we used to visit the branches, stand in the queue and wait for our turn and complete the transaction. But, in present day with time constraint, busy world none of us wants to waste time being in queue. Thanks to the internet based applications which made every work possible with a finger click. But, always a question remains how about the security to these transactions on the internet??.
The JSSE (JAVA Secured Socket Extension) is a set of packages that enable secure Internet communications. It implements a Java technology version of Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols. It includes functionality for data encryption, server authentication, message integrity & optional client authentication.
SSL configuration: SSL configuration help us in making secured communication between the application deployed inside the websphere and external client (browser) by encapsulating the data as required by JSSE. These certificates inside the websphere are mainly of 2 different types. They are as follows:-
(a) Self Signed certificates ( or Internal or Default Certificates)
(b) Signer Certificates (or Digital Certificates)
Self Signed Certificates: From websphere application server 6.1 onwards the self signed certificates are created automatically during the profile creation .i.e., whenever the profile is federated to cell self signed certificated are created automatically. The management of these self signed certificates is automatically taken care. The expiration of these certificates is monitored on a pre-defined schedule with notifications sent to system logs and email-sending capabilities. The certificates will be automatically replaced before expiration, by default, and, there will of course be a warning prior to the certificate replacement.
Signer Certificates: A signer certificate represents certificate and public key associated with some personal certificate. The signer certificate explicitly trusts connections made to or by the owner of the associated personal certificate. The signer certificate is typically made completely public by the owner of the personal certificate, but it’s up to the receiving entity to determine if it is a trusted signer prior to adding it to the trust store.
Following are the steps involved for installing the SSL signer certificates:-
1) **Invoke the ikeyman from the profiles bin directory.
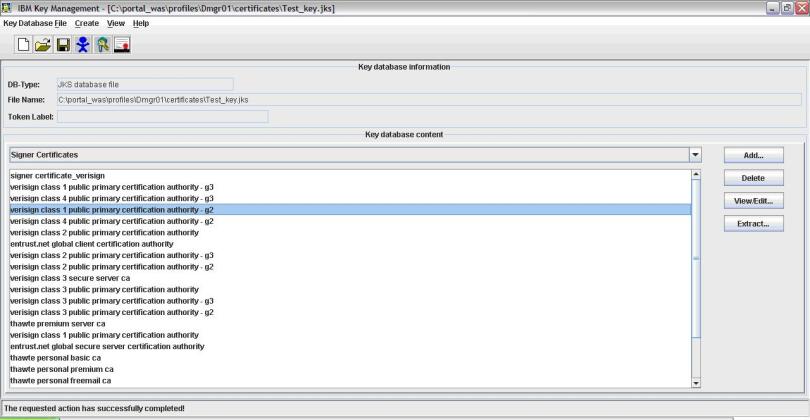
2) In the IBM Key Management Utility, click on Key Database File and then New
3) Choose Key database type and select JKS. Give any name to keystore like Test_key.jks.
4) Click the Browse button and give location where we want to store keystore file.
5) Click OK. Enter a password and click OK.
6) Click Create then New Certificate Request to bring up the Create New Key and Certificate Request window.
7) Type a Key Label, Common Name, Organization, Locality, State, and select a Country. Select 1024 for Key Size.
8) Click on Key Database File and then Open. Locate the keystore file that you created when you generated the CSR. Type the password and click OK.
9) Select Signer Certificates from the pull-down list.
10) Click the button to Add…
11) Login to WAS console with the valid credentials and Expand “Security” link at left hand side pane.
12) Click on “SSL certificate and key management”.
13) Click on “SSL configurations” link.
14) Click on “Key stores and certificates” link.
15) Select the scope by clicking on CellDefaultTrustStore (or NodeDefaultTrustStore) link from the list.
16) Click on “Signer certificates” link.
17) Click on Add button.
18) Give alias name as “Test_Cert”.
19) Give filename as complete path of “Test_Cert.cer” on server.
20) Click apply and then OK and restart all the WAS server instances.
Regards,
Weblogic-wonders Team











Great article shankar!! m sure its going to help a lot of people
TQ
Thanks sir, helped me a lot!!
We are glad that it helped 🙂
Glad i found to the point information. thanks 🙂
It helped me a lot..thanks sivaaaaaaaaaaaaaaaaa
Do you need to restart for adding public cert
yes Pulla.. you will have to restart..